Products
Building Cyber Resilience in a Complex World
In today’s digital world, cyber threats continue to evolve in scale, sophistication and impact. Organizations require more than theoretical security controls — they need proven readiness, trainings, tested response capabilities and confident leadership during cyber incidents.
We deliver practical, intelligence-driven cybersecurity services that help organizations anticipate threats, validate defenses and build lasting cyber resilience. Our comprehensive security frameworks protect critical assets and ensure operational continuity.
Proven Readiness
Tested response capabilities and confident leadership during cyber incidents ensure your organization is always prepared.
Continuous Monitoring
24/7 real-time visibility across all your digital assets, from IT and OT networks to cloud environments.
Expert Talent
Our team of seasoned cyber professionals delivers intelligence-driven services that build lasting cyber resilience.
Active Defense
Threat Intelligence & SOC operations running 24/7
Comprehensive Security Solutions
Four pillars of cyber defense, engineered to protect your most critical assets and ensure operational continuity in any threat environment.
- Train. Test. Triumph.
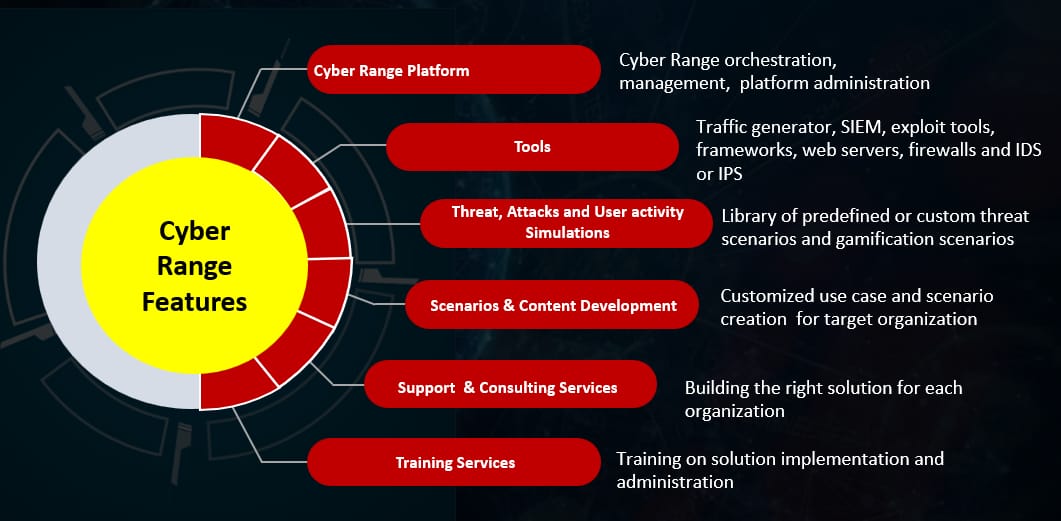
Cyber Range
Our Cyber Range delivers immersive, hands-on cyber warfare environments for Red, White, and Blue Teams. Simulate real-world attack scenarios, benchmark performance, and build a battle-hardened workforce through practical training and competitions.
- Cyber War Games – Red, White & Blue Teams
- Product Evaluation & Performance Benchmarking
- Cyber Education – Offensive / Defensive Training
- Recruitment & Talent Hunt (Cyber Induction as Service)
- National & International Cyber Competitions & Hackathons
- Integrate. Automate. Defend.
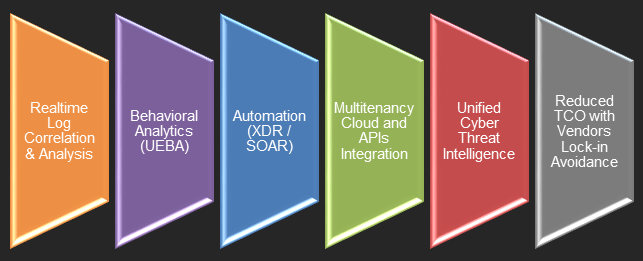
Defence Fusion
Our solution integrates threat intelligence, security operations (SOC) and incident response into a single, automated platform to proactively detect, analyze and mitigate threats. AI-driven analysis reduces MTTD and MTTR dramatically.
- Realtime Log Correlation & Analysis
- Behavioral Analytics (UEBA)
- Automation (XDR / SOAR)
- Multitenancy Cloud and APIs Integration
- Unified Cyber Threat Intelligence
- Reduced TCO with Vendors Lock-in Avoidance
- See Everything. Miss Nothing.
Eagle Eye NMS
Our Network Monitoring System provides real-time visibility into the health, performance and security of network devices, servers and traffic. Using protocols like SNMP and ICMP to track uptime, bandwidth and resource utilization.
- Real-time Network Health Visibility
- SNMP & ICMP Protocol Support
- Uptime, Bandwidth & Resource Tracking
- Automated Bottleneck & Failure Alerts
- Unauthorized Change Detection
- Centralized Multi-Environment Dashboard
- One Direction. Total Protection.
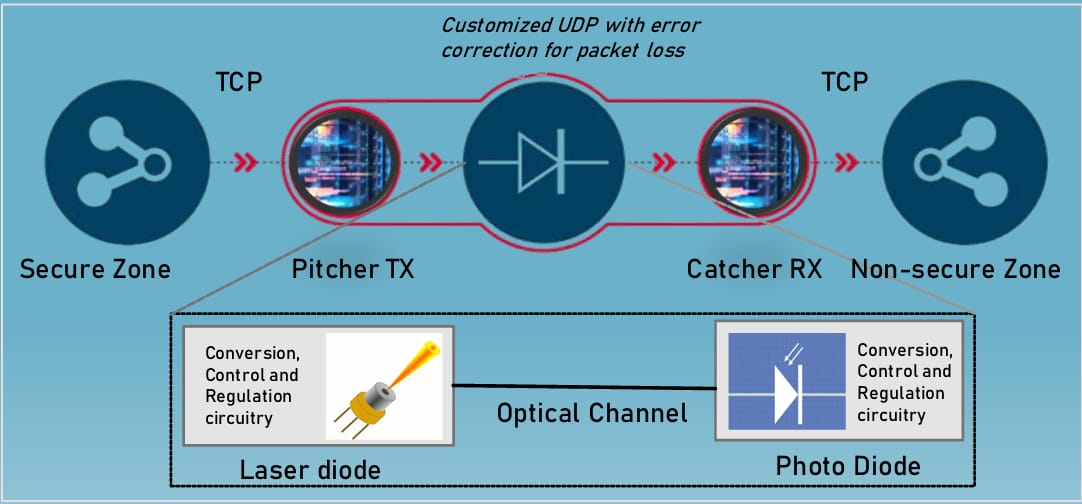
Data Diode
Our hardware-based cybersecurity solution enforces a one-way, unidirectional flow of data between networks, physically preventing return traffic. Primarily used to protect high-security ICS/OT environments from external inbound cyberattacks.
- Hardware-Enforced Unidirectional Data Flow
- ICS/OT Protection from External Attacks
- Customized UDP with Error Correction
- Pitcher TX & Catcher RX Architecture
- Optical Channel Transmission
- Zero Risk of Data Leakage
Industries & Potential Customers
Our solutions are purpose-built for the unique security demands of diverse industries, from critical infrastructure to financial services.
MSP
Managed Service Providers
Single Pane of Glass
Centralized monitoring of hundreds of different client environments from a single pane of glass. Scale security operations efficiently with multi-tenancy support.
Multi-client dashboards
Automated reporting
Centralized threat management
FinServ
Financial Services
100% Uptime. Zero Compromise.
Ensuring 100% uptime for transaction servers and maintaining strict security compliance for audits. Protect financial data and meet regulatory requirements.
Transaction server protection
Compliance & audit support
Fraud detection
Health
Healthcare
Real-time monitoring of IoT medical devices and protecting sensitive patient data infrastructure. Ensure continuity of critical care while meeting data privacy requirements.
- IoT medical device monitoring
- Patient data protection
- Regulatory compliance
Telecom
Telecommunications
Tracking massive volumes of high-speed network traffic across geographically distributed towers and data centers. Maintain service quality and detect anomalies instantly.
- Distributed infrastructure visibility
- Traffic anomaly detection
- Tower & data center coverage
ICS/OT
ICS and OT
Industrial Control Systems and Operational Technology environments used to monitor and control physical processes in critical infrastructure, including manufacturing, energy and utilities.
- Manufacturing security
- Energy & utilities protection
- Physical process monitoring
Cybersecurity Services Offerings
We deliver practical, intelligence-driven cybersecurity services ranging from proactive assessments to 24/7 real-time monitoring, rapid incident response and digital forensics.
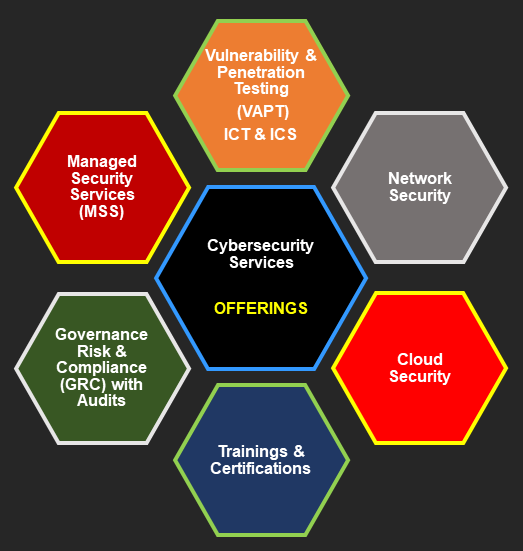
Intelligence-Driven Security Services
We deliver practical, intelligence-driven Cyber Security Services that help organizations anticipate threats, validate defenses and build lasting cyber resilience.
We can consult to protect digital assets including data, IT or OT networks and systems from unauthorized access and malicious attacks.
VAPT & GRC
Proactive Assessments
24/7 SOC
Real-time Monitoring
< 15 min
Response Time
Expert DFIR
Digital Forensics
VAPT
Vulnerability & Penetration Testing
Comprehensive VAPT for ICT and ICS environments. Identify and remediate security weaknesses before adversaries can exploit them.
MSS
Managed Security Services
24/7 outsourced security monitoring, management and response. We act as your dedicated security team, always on guard.
Cloud
Cloud Security
Securing cloud environments, workloads, and APIs. Protect your cloud-native applications and infrastructure from modern threats.
Network
Network Security
End-to-end network security solutions including firewall management, intrusion detection, and traffic analysis for complete perimeter defense.
GRC
Governance, Risk & Compliance
Comprehensive GRC programs with audits to ensure your organization meets regulatory requirements and industry standards.
Training
Trainings & Certifications
Hands-on training programs and certification preparation for security professionals. Build a skilled, resilient cyber workforce.
DFIR
Digital Forensics & Incident Response
Rapid investigation and response to security incidents. Preserve evidence, contain threats, and restore operations with minimal downtime.
Need a Custom Solution?
Our experts will craft a tailored security strategy for your specific needs.
Comprehensive Security Solutions
Four pillars of cyber defense, engineered to protect your most critical assets and ensure operational continuity in any threat environment.
Get in Touch
USA
47396 Middle Bluff Pl, Sterling, VA 20165-3129, USA
Phone
+1 (347) 708 – 0289
